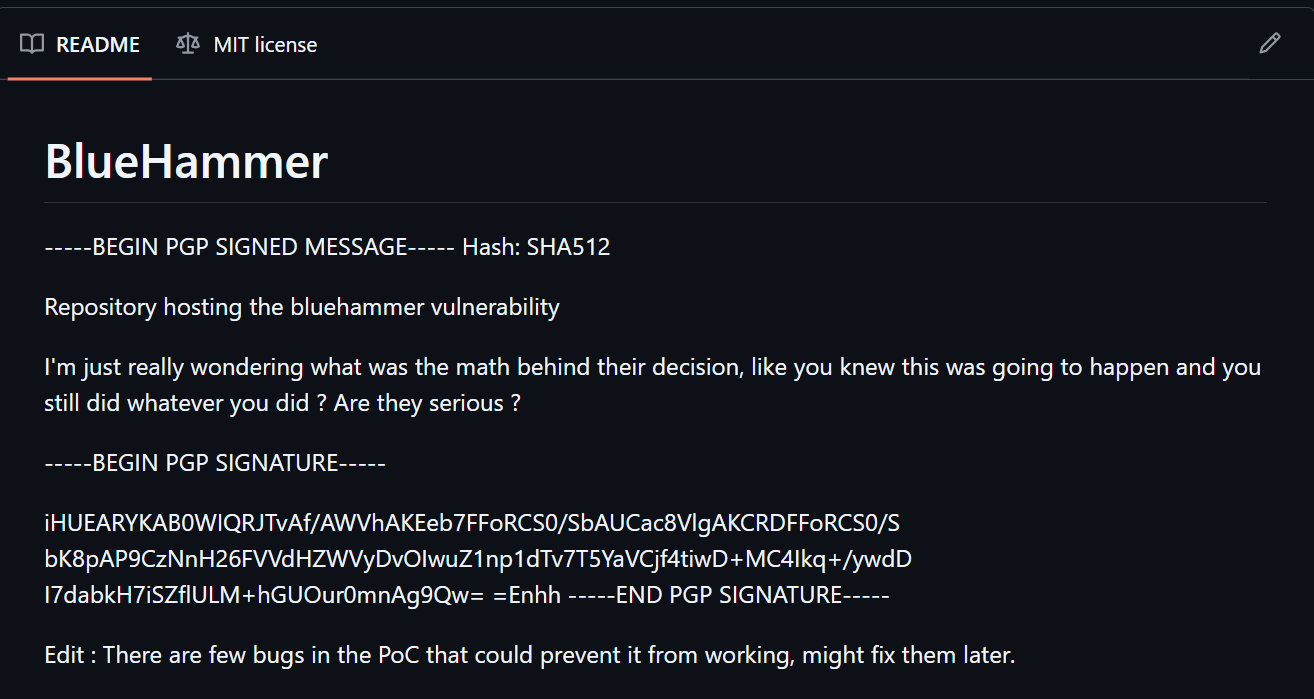
On April 2, 2026, a security researcher using the name Chaotic Eclipse published a blog post stating that they were “doing it again.” Under this warning, a link to a GitHub account page for a user named “Nightmare Eclipse” containing an exploit known as BlueHammer.
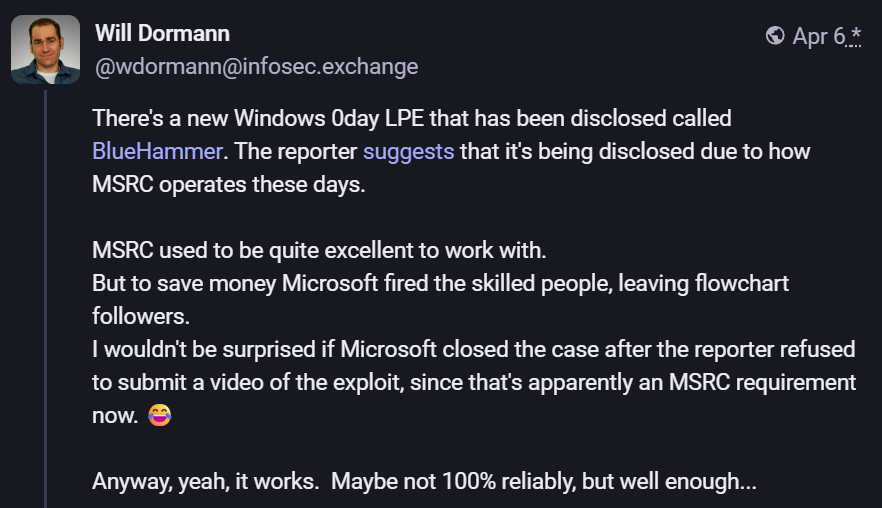
BlueHammer, as it turns out, is a zero-day Windows exploit, meaning it was released into the wild ahead of any Microsoft action. BlueHammer has been confirmed to work by Will Dormann, a principal vulnerability analyst at Tharros (via BleepingComputer).
Article continues below
Microsoft Security Response Center takes the blame; Microsoft responds
The worst part about the BlueHammer incident is that, according to the leaker, it apparently could have been prevented. In the original blog post, the frustrated security researcher stated:
“Unlike previous times, I’m not explaining how this works, y’all geniuses can figure it out. Also, huge thanks to MSRC leadership for making this possible!!! And special thanks to Tom Gallagher!”
The Gallagher mentioned in the jab is assumedly the VP of Engineering for MSRC. The jabs don’t stop there, continuing on the BlueHammer GitHub page.
“I’m just really wondering what was the math behind their decision, like you knew this was going to happen and you still did whatever you did? Are they serious?”
Judging by these semi-vague statements, whoever leaked the BlueHammer exploit attempted first to privately work with the MSRC in order to get the issue fixed, but became fed up.
Dormann, who confirmed the exploit, shared some interesting words on Mastodon on April 6.
“MSRC used to be quite excellent to work with. But to save money Microsoft fired skilled people, leaving flowchart followers. I wouldn’t be surprised if Microsoft closed the case after the reporter refused to submit a video of the exploit, since that’s apparently an MSRC requirement now.”
The BlueHammer incident isn’t a good look for Microsoft’s main line of defense against zero-day exploits. Of course, it’s nigh impossible to confirm that the leaker actually reached out to Microsoft’s Security Response Center team before posting the exploit on GitHub.
In a response to BleepingComputer, added to the original article covering BlueHammer, a Microsoft spokesperson said this:
“Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible. We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community.”
It’s a rather boilerplate response, and security communities are understandably upset about the leaked exploit and Microsoft’s perceived incompetence.
Over on GitHub, the BlueHammer exploit has, at the time of writing, some 1,200 stars and 425 forks. This essentially means that at least 425 people have taken it upon themselves to modify the code for who knows what reasons.
Microsoft promised to make Windows 11 better, so why did MSRC allegedly drop the ball?
A zero-day exploit like BlueHammer released into the wild is one thing, but when it’s claimed to be in response to MSRC incompetence, it’s something else entirely.
Microsoft has been putting a lot of resources lately into improving Windows, mainly in response to sustained negative feedback that’s often turned into outrage from the community.
While the EVP of Windows & Devices at Microsoft, Pavan Davuluri, has promised his team is “focusing on making Windows 11 more responsive and consistent” by way of “improving system performance, app responsiveness, File Explorer and the Windows Subsystem for Linux,” it won’t mean much if Microsoft can’t properly stay ahead of serious threats.
A zero-day exploit like BlueHammer released into the wild is one thing, but when it’s claimed to be in response to MSRC incompetence, it’s something else entirely.
On my mind is news about Claude Mythos, a new AI model that recently proved it could identify cybersecurity vulnerabilities that had gone unnoticed for decades. It was so powerful that it caused cybersecurity stocks to fall off a cliff, and it has since been put back into a cage by its Anthropic overlords while governments figure out what to do about the perceived threat.
If Microsoft has indeed gutted its MSRC team, as posited by Dormann, I don’t doubt that Windows could be in serious trouble as security threats evolve.
Microsoft raked in about $281 billion in revenue in 2025. Surely more of that can go towards keeping the MSRC, which has been a key proponent of Windows development and upkeep since 1998, in top form.
BlueHammer was killed in a recent Windows update, but it was live for nearly two weeks
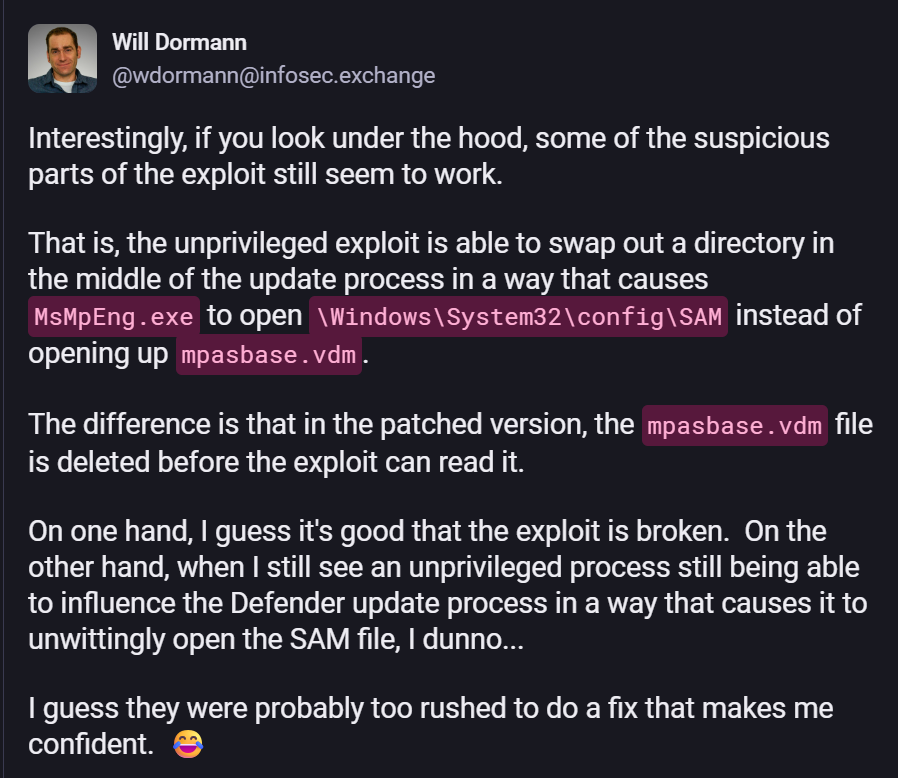
I’ve been following Will Dormann’s updates regarding BlueHammer, and he recently posted proof that the exploit was killed in the latest Windows 11 CVE-2026-33825 update from April 14, 2026.
Dormann notes that the “exploit doesn’t get past the point where it makes a symlink within the Windows object manager.” However, he also notes that “if you look under the hood, some of the suspicious parts of the exploit still seem to work.“
So, yes, the exploit is technically broken after the Windows update, but some of the nasty bits remain.
What do you think about the BlueHammer incident?
All signs point to Microsoft’s Security Response Center failing to act when it was presented with BlueHammer exploit details. Do you think the leaker is lying and is instead attempting to libel the company?
Or are you of the mind that security researcher Will Dormann is correct when he says that Microsoft gutted the MSRC program, which led to the leak after official channels failed to act?
Let me know what you think, including any first-hand experience you have with MSRC, in the comments section below.

Join us on Reddit at r/WindowsCentral to share your insights and discuss our latest news, reviews, and more.